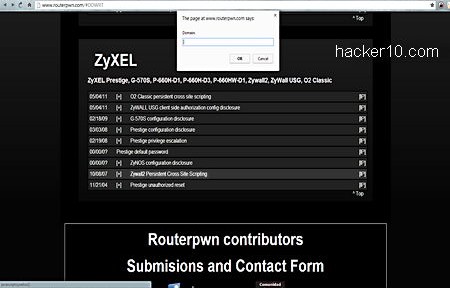
Routerpwn is a web application listing dozens of ready to run local and remote exploits for, largely, home routers. It covers all major brands, all you have to do to test if your personal router is vulnerable to one of the exploits is to search for the make and model of your router and click on the exploit name to execute a javascript window testing a known vulnerability that will automatically break into the network or open up the default router IP, 192.168.1.1 and try a default admin password or privilege escalation.
To learn more about the exploit click on the plus sign next to the listed bug and you will be taken to a security list like SecurityFocus or Seclist displaying full details of the exploit and the date it was first discovered.
The site also contains links to lists of default router administrator username and passwords. Another tool can be used to find out an Access Point vendor entering the MAC address of the device, which hex number can be discovered with a simple network scan.

It is not necessary to be connected to the Internet to use Routerpwn, the site can be stored offline, javascript exploits in local routers will work regardless of Internet access.
Exploiting a router does not necessarily mean to be able to get into the network finding out a WPA key, some of the exploits in Routerpwn launch a denial of service attack against a router by pinging it non stop and bringing down the whole network. Other exploits show your router configuration, some vendors store keys to reset passwords in plain text inside configuration files that can be seen by mistake using a cross site scripting attack.
There was an Android application for Routerpwn in Google Play but that link has now been removed, however the website can be accessed from any mobile device or game console that has an Internet browser. Everything has been optimized for access on the go coding it entirely in HTML and javascript.
New exploits can be submitted to the site and if you would like to find out your own router vendor, the URL http://www.routerpwn.com/detect.html will show you the brand, if it can’t identify it a form will come up inviting you to submit the information.
Routers are seldom upgraded or flashed by home users, even a exploit that is a few years old will still work against many devices. Routerpwn is a very powerful tool for penetration testers for a very important often overlooked security item that antivirus software does not screen.