jTorchat, standing for Java Torchat, is a rewrite of Torchat, a decentralized anonymous P2P messenger that works over the tor network. Being written in Java means that the code is easily carried across platforms, jTorchat should work in any operating system that has Java installed (Linux, Windows, BSD, etc), it can be used in portable mode but my Windows7 OS asked me for administrator rights to grant access to Java and allow the application through the Windows firewall, it will possibly won’t work in computers where you do not have admin rights (i.e. library, internet cafe).

The settings allow you to change language interface, make links clickable, sync your buddy list and automatically start file transfers saving them to the Downloads folder, the rest of the messenger has expected basic features consisting of announcing status as away or online, adding contacts, request buddies, blacklist people and what they call “Holy contact” which means whitelisting someone, a flashing message on the Windows taskbar will warn you everytime someone joins the chat.
At the moment there are no chatrooms but you can easily interact with other people who have marked themselves as online or broadcast a message to a whole group marked with an specific hashtag, like #linux, #torchat-help, #public, #privacy. It is also possible to use other chat commands like /nick or /help and retrieve a webpages from your buddy using the /page command but there is no support for images or html, only .txt.

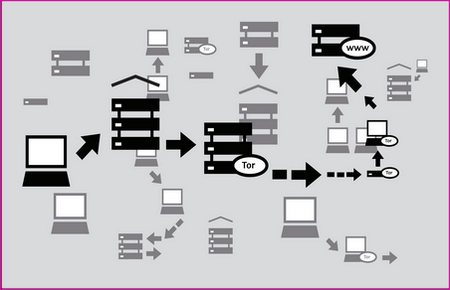
All users get a unique alphanumeric string randomly created by tor, based on the .onion address of a hidden service, this string is used to communicate with your buddies so that tor knows where to send the messages. jTorchat local port can be changed to any unused one and it can work with obfsproxy, a tool hiding the nature of the traffic to circumvent tor proxy blocking at ISP level by some countries.
There wasn’t too many users when I visited jTorchat but they are relatively new and as the tool is better known it could change, something to be aware of is that you will still be browsing the Internet with your home IP, jTorchat will only route through the tor network your online chat session, be very careful if you click on a link posted by someone else in the chat.