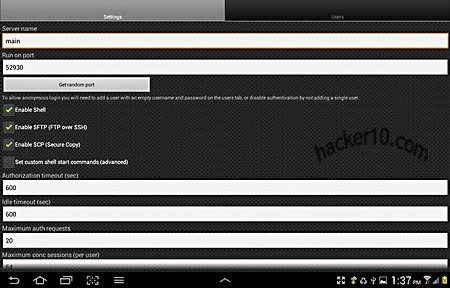
SSH Server is a complete Secure Shell daemon, Secure FTP, Secure Copy and Telnet server Android app that doesn’t need rooting the device. After installing the app you will be able to enter an SSH server hostname and port, with optional public key encryption authentication instead of password and allowing X11 forwarding, a way to grant graphical information to pass through firewalls, giving you a graphical interface if the Unix server you are connecting to supports it.
Logging is very detailed, in verbose mode it includes filters and email logs, to save space it can be set to only record errors leaving connection logs out, the server is accessible from the Internet and you can whitelist IP addresses blocking everyone else.
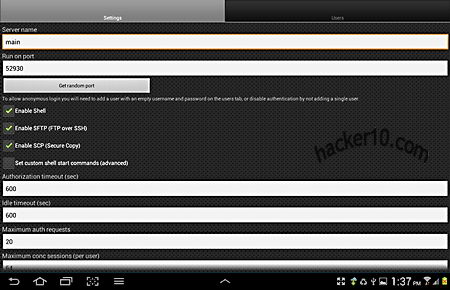
The free version of SSH Server only allows for one server, it should be enough for most people, to connect to the server just use SSH command line from shell like you would do in Linux, in the form of:
ssh -v -l USERNAME ADDRESS -p PORT
With -v being for verbose -l for login and -p indicating the port, the server address should be the IP, the app supports dynamic DNS setting a permanent custom hostname that you can access, remaining always the same even if your device IP changes, companies like DynDNS can provide this service. There are other Android apps like Dropbear providing SSH capabilities to your phone but it requires root, and there is the connectbot app too but this SSH Server from Icecoldapps is the most complete, it comes with SFTP combined with SSH.