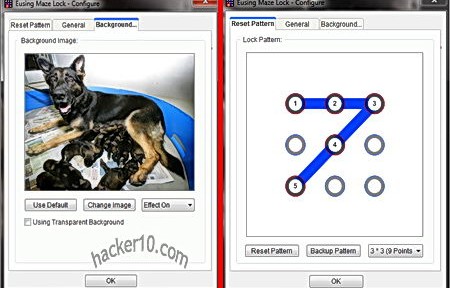
Eusing Maze Lock is a free pattern based screen lock to stop people from accessing your computer while you are away, the unlocking mechanism consists of nine dots inside a grid that have to be connected in a certain order with the mouse to unlock the screen. This type of screen lock is often found in smartphones, it is commendable for this company to bring a security tool that does not require you to remember yet another password. The unlocking pattern is easy to remember if you use it daily, otherwise a back up copy can be kept in a safe place, or uploaded to your email account so that if you forget the unlocking pattern diagram you can restart your computer or look at the online back up copy using another device.
The program will autolock the computer when idle, the background lock can be transparent or set to any image of your choice, the configuration tab allows you to specify the inactivity period before the computer screen locks, and optionally lock the keyboard or disconnect the computer from the Internet when the screen lock is activated, this stops people from messing around with your data if you have a document open in the background. If anyone attempts to get into your computer using the wrong pattern code a loud alarm siren sounds displaying a custom message on the screen and the computer will go into lock down for in between one and three minutes before any other unlocking attempt can be made, or alternatively the machine will shut down, the choices can all be set inside the configuration tab.

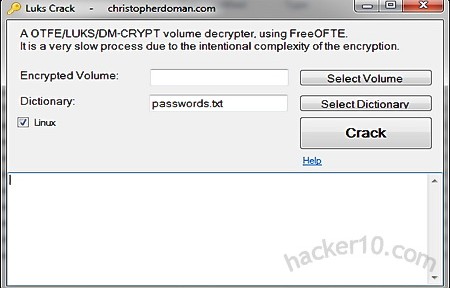
This is an excellent screen lock that does all you need to protect a computer located in a shared room, but if your adversary is a state or corporation entity they will have the resources to acquire professional computer forensics software, like Passware Kit Forensics, able to get through any screen lock in a matter of seconds using your USB port and the autorun feature to execute a script mirroring your hard drive data or extract RAM memory even with the computer screen locked. If you adversary is low level, Eusing Maze Lock is hard to beat as a free and secure screen locker.