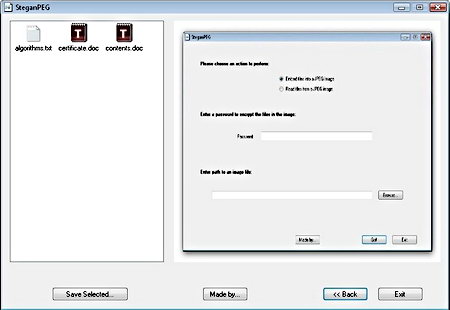
AxCrypt is a free open source encryption program for Windows computers available in 32-bit and 64-bit versions, after installing AxCrypt it will integrate with your right-click menu and allow for single click encryption, it is very easy to use, there is nothing to configure, everything works straight out of the box after installation, you can right-click on a folder and instruct AxCrypt to encrypt the entire contents, the program will then create multiple encrypted file belonging to each one of the files inside.
The software interface is multilingual, available in 7 different languages, it can be used from the command line and a portable version of AxCrypt is available for those on the go wanting an encryption programs that runs from inside a USB thumbdrive.
There is no maximum file size for encryption, the only size limit comes imposed by your operating system boundaries on file size, AxCrypt runs on very low resources, to use AxCrypt you only need 5MB RAM, 2MB hard disk space, temporary disk space 1.5 the size of the file being encrypted, and a low end computer desktop CPU.
Because AxCrypt is open source, you can download the source code and compile the program yourself where you to feel inclined, you could check the source code for backdoors before compiling it.
AxCrypt encryption method
AxCrypt uses the AES algorithm with 128-bit keys for file encryption and SHA-1 for hashes, there is no backdoor, if you forget your password that is it. The AES encryption algorithm that AxCrypt uses was selected by NIST (American Nations Institute of Standards and Technology) after a 5 year process in which fifteen competing designs were presented, AES is the current Federal USA Government standard algorithm for encryption.

Files encrypted with AxCrypt have the extension .axx, it retains the original file name and information, you can rename the file if you want to disguise a descriptive name, temporary files are automatically shred, the encryption keys are not stored in Windows page file. If you don’t want to erase the file after encryption you can just choose encrypt copy from AxCrypt menu.
To make it more difficult for an attacker to brute force your password and make the best of the full 128-bit encryption strength potential that AxCrypt offers, you should be using with a meaningless passphrase sequence of 22 characters, if you decide to create a keyfile with AxCrypt and use it for encryption your files will automatically be secured at the maximum level, the keyfile encryption method can be used in conjunction with a password.
AxCrypt software developers recommend that you always create a keyfile for encryption, the created keyfiles are made of 256 bits encoded in Base64, they are saved as a .txt text file with random characters in it.
AxCrypt file decryption
When sending your encrypted file over email to someone else that person will need AxCrypt installed to decrypt it, there is a free program called AxDecrypt that allows others to view AxCrypt encrypted files without installing the full software, AxDecrypt only serves to open files with the .axx extension and it can not encrypt.
You can choose to create .exe self-decrypting files, the other end does not need any kind of program to view the encrypted data, they just need to know the password used, one downside is that .exe files many times contain viruses and few people trust them, antivirus could flag them as a malware, and some email services like Gmail do not accept the sending of .exe file attachments.
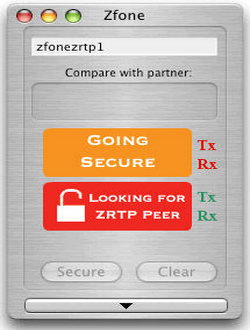
Like all symmetric encryption software when you send an encrypted file to someone he/she will need to know the password you are using, you can transmit the password over a secure channel, ideally in person and if that it is not possible then using an encrypted VoIP call, or an Internet messaging program with built in encryption.
File encryption vulnerabilities
While AxCrypt contains no backdoor and the algorithm it uses can not be cracked at present, all file encryption programs have side vulnerabilities residing on the operating system, this is what you should watch out for.
- Weak password, file encryption programs are only as good as your password
Solution: Use a very hard to guess passphrase not contained in a dictionary or use a keyfile to secure your files, use a password manager if needed to remember it.
- Temporary files and backup copies stored by the your operating system while viewing the decrypted file
Solution: Use data wiping software in conjunction with your file encryption software, routinely wipe Windows locations where temporary files are normally stored, like for example the Windows page file, quality data wiping software come already preconfigured to securely erase those locations.
- Your computer has a keylogger installed that captures your password
Solution: Have an updated antivirus and use a high quality firewall that will warn you of outgoing connections, the default Windows firewall will not do this.

After decrypting a file AxCrypt will automatically overwrite it, secure data wiping consists of a single pass using pseudorandom data, this is enough to protect you from common undelete software but it will not protect you from expensive special diagnostics hardware used by well funded adversaries like corporations and law enforcement, if you need that level of protection get a different encryption software because data could be recovered from previously erased data.
AxCrypt online documentation is very complete, if you want to know the inner workings visit their homepage, if you get stuck, they have an online forum and a mailing list where to ask questions to other users.
Conclusion on AxCrypt file encryption
It doesn’t have the prettiest of interfaces and its configuration capabilities are next to none, while some might view this as a disadvantage, others will see it as an advantage because it makes operation very easy to understand for beginners.
AxCrypt strong points are that it is open source, it contains no backdoor, it uses a standard uncrackable algorithm for encryption (AES128) and it is easy to operate, its interface could be improved but it gets the job done, this is an excellent program for those on a budget because it is free (donationware) and it will securely encrypt your files.
I would not hesitate recommending AxCrypt to friends in need of secure encryption software but the single pass temporary data overwriting was disappointing, if you are a business user stay out of AxCrypt because it is only secure enough for the home user due to this.