SNOW is a free program to hide messages inside ASCII text, for those who don’t know ASCII stands for American Standard Code for Information Interchange, a binary scheme to represent English characters in computer language that can be read by nearly all text editors although UTF-8 is replacing ASCII as the world wide web language, ASCII is the default format to save text in Unix and DOS operating systems.
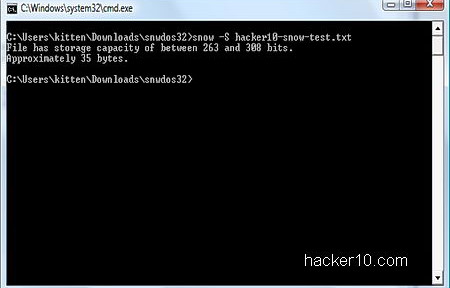
The program is a tiny command line based utility of just 60Kb, downloadable as Windows executable or Java applet to work with other operating systems like Linux. SNOW comes with a manual listing the available commands and real examples. Do not be scared of the command line, it is not hard to use. The source code is also available for download so that others can review it.

SNOW steganography takes advantage of white spaces found in text messages and hides invisible text inside them, this keeps the visual embodiment and does not raise any suspicious to watchful eyes. Security is heightened with compression to fit more text inside the white spaces and text encrypted with ICE, an open source symmetric 64-bit block cipher designed by the same author to withstand cryptanalysis and guard from detection.
This is a superb unexpected way to send secret messages to other people with the only downside being that, unlike messages hidden in photos that can be distributed uploading them to public online photo albums, you can not copy and paste steganographic SNOW text messages on a website because the data is hidden inside the white spaces. You will have to necessarily send the full ASCII file text to your contact, revealing metadata, like who is talking with who. But you could upload an innocuous compressed file, e.g. video, with ASCII text instructions included and hide the message inside the text white spaces, this would waive the need of emailing anybody and it would not ascent mistrust.
SNOW has been around since the nineties and has recently been released under the Apache license, it is a very well documented tool with technical cryptanalysis information about its design as well as benchmarks.