UPDATE 2015: Read Police arrest Freenet user! This software is not safe!
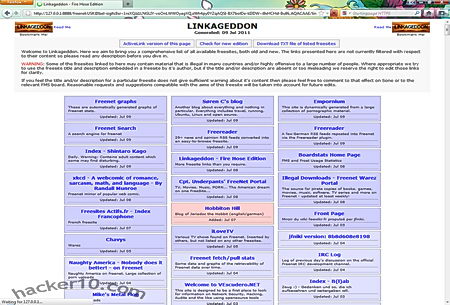
Freenet is a free P2P software designed from the ground up for anonymous file sharing, it is targeted at those who want to exercise free speech without fear of censorship or retribution, besides anonymous filesharing Freenet also lets you to publish websites and take part in online bulletin boards that are only accessible to those who use the software.
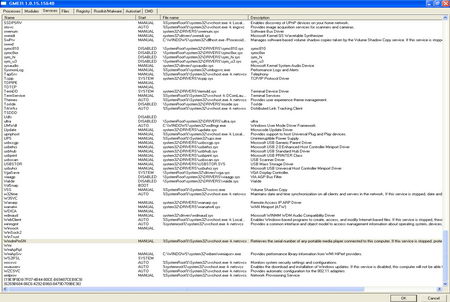
The network is decentralized without any central hub, shared files are stored encrypted in different computers around the world, the default folder where shared files are stored is called “datastore“, the size of this folder, just like bandwidth made available, is determined by the user during installation and it can go from a few Megabytes up to dozens of Gigabytes. Because all the stored data is encrypted Freenet users do not know what they are sharing and have no saying on what is being shared, this allows for denial of knowledge, while some people will be sharing Linux distributions, others could be storing copyrighted work but they will not be aware of it because the contents in the disk are encrypted and the user can not see them, communications in between nodes is encrypted too.
Files in Freenet are kept or deleted depending on popularity, if something isn’t downloaded for some days, Freenet will make way for new uploads.
How to Install Freenet
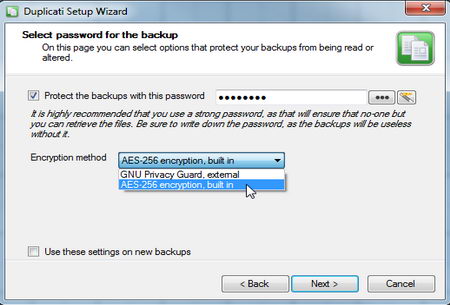
The software is a small 13MB download and it is recommended that you have 650MB of free disk space to store the files being shared, different languages can be chosen during installation, I would recommend you to change the default installation directory somewhere else easy to find, the default folders is set to install in between Windows system folders.
Once you have installed Freenet, if you have a proper firewall blocking outgoing connections (ie not Windows firewall), you will get a few warnings about Java attempting to access the Internet, you will need to authorize this, after that your Internet browser will launch and a wizard will guide you during the set up of your Freenet node, it took me no more than 5 minutes altogether, Freenet has no fancy GUI it operates from inside your browser but it gets the job done easily.
Note: Freenet website has been blocked by the Chinese Government for years.
How to be Anonymous on Freenet
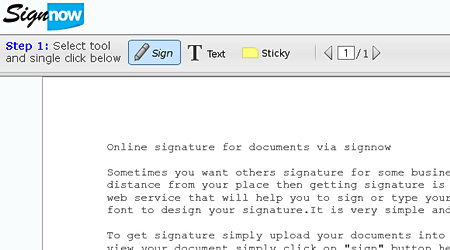
It is strongly recommended that you do not use the same browser that you normally use to surf the Internet for Freenet (Freenet runs inside the browser), a malicious script while surfing the Internet could break with your anonymity and find out what Freenet sites you have visited, Freenet works well with all major browsers (except IE), just download any other. When you first get started with Freenet you will have to use the “connect to strangers” option in order to find something of value to download, as soon as you make 5 friends on Freenet choose the high security settings called “only connect to friends“, it needs a minimum of 5 friends for this to work and it makes tracing data back to you extremely difficult.
This anonymous file sharing software include plugins to extend its anonymity service, like for example Freemail, a messaging system where mails are sent over Freenet encrypted and anonymously, Freemail makes it very difficult for others to learn who you are communicating with. Freenet plugins can be fetched over the network to get around ISP censorship (i.e. China), you should be careful about what plugins you install, these are not necessarily approved by Freenet developers and could endanger your P2P anonymity.
I attempted to use Freenet while running a VPN and Freenet stopped working, I think this is due to the TUN/TAP drivers that OpenVPN uses and Freenet might also be using, I noticed that without the VPN active Freenet forged ahead, in my experience it is incompatible to run Freenet and a VPN at the same time, however Freenet FAQ does not say anything about this, I can’t guarantee 100% it was something else.

Freenet advantadges
- Decentralized filesharing, even if one server goes down the content will still exist
- Files shared by users are stored encrypted nobody knows what they share (helps reduce legal liability)
- Self regulated filesharing software keeps popular files and erases files that nobody downloads
- Communications in between Freenet nodes is anonymous and encrypted
- Anonymous discussion boards and website publishing can be done on top of P2P file sharing
Freenet Disadvantages
- There are lots of offensive material around
- When using high anonymity settings filesharing is slow (data has to be routed around nodes)
- It can daunting for newbies, the concepts are not easy to understand
Conclusion on anonymous P2P over Freenet
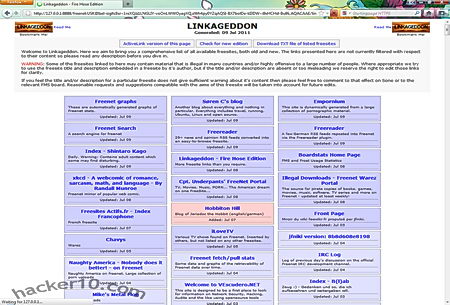
Freenet is as close as one can get to real P2P anonymity, the network can be slow at times due to the data being bounced around nodes but anonymous discussion boards, directories with links to find content, and anonymous email over the network make up for it. This is one of the best darknets that exist for anonymous file sharing in P2P, when used accurately, Freenet is for file sharing what the tor proxy is for anonymous Internet browsing.
I only found two downsides, the software can be hard to understand and speed is slow, other than that this darknet is brilliant.
Freenet speed improves a lot after a few hours! Do not give up on it due to speed, the longer you run it, the quicker downloading files over Freenet will be.
UPDATE 2015: Link to Freenet removed, this software has been cracked by law enforcement. Avoid!