Autorun is a Windows feature that indicates the operating system what action must be carried out when a drive is mounted, i.e. USB external drive, thumbdrive, CD-Rom, according to the latest BitDefender report autorun is also one of the most exploited methods to insert malware in computers, the Conficker worm for example created an autorun trojan on removable drives attached to the infected machine, autorun command, i.e. view, play file menu options, is executed without user intervention which is meant to be helpful but it carries a security risk being able to execute malware too.
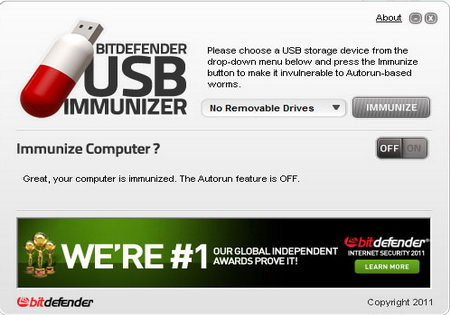
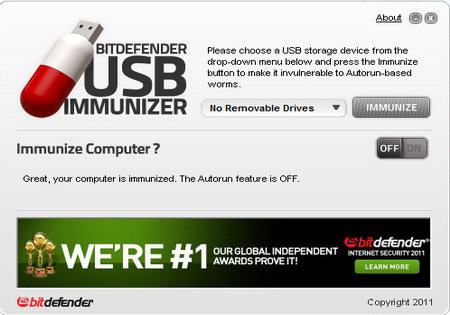
BitDefender USB Immunizer will warn you if autorun is enabled in your computer offering you to disable it with a single click, it will then create an Autorun.inf folder on your chosen drive (thumbdrive, SD card, etc) this file will stop malware from auto launching and will prevent itself from being overwritten by another program storing a hidden folder and other files inside Autorun.inf (where autorun commands are) making it hard for malware to locate and erasing it, if you ever need to erase the file yourself you can do so booting from a Linux live CD which will override windows file permissions.
An alternative to USB Immunizer preventing malware from launching exploiting Windows autorun feature is the open source project “No Autorun” which locks the default Autorun.inf file as opposed to creating its own like BitDefender does.
Leave a Reply