BCTextEncoder from Jetico is a free small portable application to encode and decode text, password protecting it with AES256-bit symmetric encryption or public encryption keys that can be either imported from a file or generated for you with the included BestCrypt Key Manager from where you can manage key pairs with the standard PKCS-12/X.509 format.
Encrypted text can be easily copied to the clipboard or saved as .txt file, the toolbar also has an envelope logo to directly send encrypted text by email opening your email client, but during my test this function did not work for me and clicking on “Send encoded text by email now” would pop up an error window. I could not fix this problem but you can still copy and paste the text anywhere you like, from Usenet clients to webmail. The only detail is that encrypted text will be appended with the line “Version: BCTextEncoder Utility“, giving away the software and version that you have used to scramble the text but it is not a security risk if the encryption is sound.
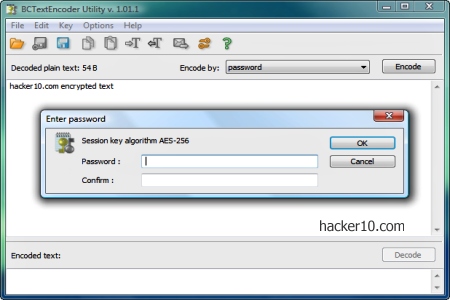
The program comes with a help file and it is very well documented at user and technical level, with a diagram explaining the encryption process. First the text is compressed with zlib, a software library for data compression, then you decide whether to use symmetric AES256 or asymmetric RSA for encryption, a third step converts the text to readable Base64, an encoding scheme to represent binary data as text, and after that you are ready to securely send the ciphered message wherever you like. Just note that BCTextEncoder only works for text, if you would like to cipher files, like images or videos, you will need a different program.
It is impressive that such a tiny program packs so many powerful features and although it is closed source, Jetico is a Finnish company that has been around for many years developing security products, which gives more peace of mind than a one man hobby program.
As usual the only challenge will be to convince the receiver to download BCTextEncoder to be able to decrypt the messages you send, this can be done with your best friend but when you have a group of people with a different operating system you are not very close to, it gets harder to agree on an encryption standard. BCTextEncoder only works in Windows.