TeamDrive is a cross platform (Windows, Mac, Linux) cloud storage service with uncrackable encryption, using AES256bit and RSA-2048 public/private key, data is encrypted in your computer before it reaches their cloud servers, Teamdrive has no way to access the files, limiting their legal liabilities since you can’t be compelled to decrypt something that you don’t have the key for, the encryption key remains in the user computer at all times.
To set up a Teamdrive account you are only required a valid email address, I liked that they have a portable version that can be carried in a USB thumbdrive or kept inside an encrypted virtual container (e.g. Truecrypt), but you will need to configure the default settings to make sure that there is no data leakage in the host computer, luckily Teamdrive software settings display the file path for data back ups and cache, a quick look will tell you where in the drive it is kept.
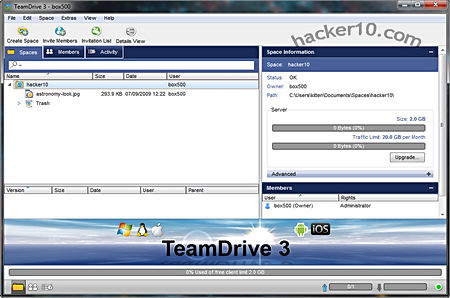
The program is divided intro three tabs, “Spaces“, where you can create folders, organise your files and set access permissions for other members and with a right click send an invitation via email revealing the URL for the data you would like to share with others, optionally, spaces can be password protected. Another tab called “Members” lets you see who has access to a particular space and a third tab called “Activity” contains a very detailed log of file movements, like uploads and downloads with timestamps. To add files, manually select them or drag and drop inside the window, everything is quickly sync when there are changes, a trash can will save erased files that can be restored if you change your mind.
Inside settings you can configure a proxy if you are using it to access Teamdrive cloud storage space, the paid for version allows you to assign roles to other people, setting up administration rights, like being able to publish and delete files or remove other members from a shared space. There is support for smartphones, you can run the application in Android or iPhone The free version has limited storage space and bandwidth, indicated inside the application with a graph bar, enough for light file sharing.
Teamdrive is a decent alternative to SpiderOak and definitely better than Dropbox, where the company can decrypt your data, if you care about privacy drop Dropbox now.