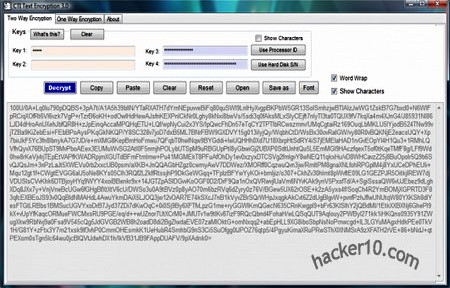
Open source CTI Text Encryption is a small (290Kb) portable application to secure your text messages, there is no need for administrator rights and it should work in any public computer, I found a few of the default settings confusing, like for example naming the password fields “Key” and having everything hidden with asterisks by default, you will have to tick the “Show Characters” checkbox to see what you are doing, on a public computer is best to keep everything hidden obviously. It took me a couple of minutes looking around to familiarize with the software.
The program has two encryption tabs, “Two way Encryption” and “One Way Encryption“, the later is not reversible and can not be decrypted, the only possible use seems to be hashing a text message (creating a number generated from a string of text), it can be useful as anti-tampering measure to ensure message integrity, the output result can be copied and pasted with the a message.

The software allows you to use your computer processor ID or hard drive serial number as a password with a single click but anyone with access to your computer could find those out, I did not find the feature too secure for that reason and there is no particular advantage that I know of by using them instead of a traditional password.
CTI Text Encryption could be useful for travellers, assuming you convince the receiving end to download and use the same software to be able to read your messages. If you travel often it’s best to sign up with an email service that offers encryption by default, but unless you have your own computer security is easy to compromise, and if you use your laptop with a Wifi connection, PGP or GPG encryption would be the best option.
I couldn’t find much information about CTI Text Encryption inner workings other than some change logs mentioning SHA256, Twofish and the Rijndael Algorithm (AES) .