If a computer has been infected with a virus and refuses to boot or when it does malware kicks in stopping you from running a virus scanner,using an antivirus live CD will bypass the need to boot the operating system helping you to remove any callous rootkit. There are various Linux based live CDs that allow for data recovery, the antivirus live CDs below have specifically been designed to remove persistent viruses and they are user friendly, meant to be used as a last resort when everything else fails or to save you time if you are a computer administrator.
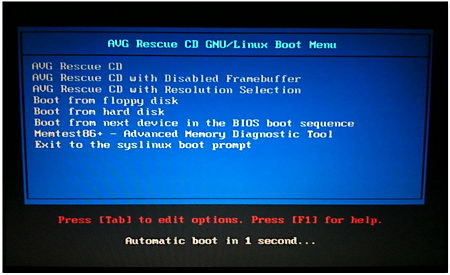
To use an emergency recovery disk all you have to do is to burn the .iso to blank media, insert the CD rom inside the optical drive, reboot your computer making sure CD-drive is the first booting device in the BIOS and you are in, the live CD will scan your computer for viruses once it boots.
Dr Web live CD: When you boot the CD it detects all disk drives automatically without the need to mount them, you can select a folder or disk to be scanned, the included Midnight Commander file browser allows you to copy any file to an external device and help is available from Dr. Web by email. This live CD lets you check your RAM memory for errors with the Memtest86+ utility making sure that your problem is not a hardware fault.
AVG Rescue CD: It comes with antivirus and antispyware, it defines itself as a portable version of AVG antivirus inside a Linux distribution, you can use it to move files to an external device, test RAM memory, edit registry keys and ping network devices to see if they are reachable, everything is free and it comes with the latest virus signatures database.
PCTools live CD: Officially named Alternate Operating System Scanner, this antivirus live CD will detect and remove rootkits and other difficult to delete malware, it uses the Spyware Doctor antivirus engine to scan your files and Windows registry, if it finds something it cleans it up warning you of the location and the virus name.
F-Secure Rescue CD: A customized Knoppix Linux distribution made by F-Secure to remove persistent malware, any virus you have in your operating system will be useless against F-Secure Rescue CD, first of all because it runs on Linux and secondly because the operating system in your main hard drive will not be active, the live CD can be used for data recovery too.

Avira Rescue System: Linux based live CD to scan your computer for viruses, Avira antivirus database is updated several times a day, this is a good live antivirus CD to catch the latest exploit, once malware has been detected the live CD will automatically remove it saving yourself time reinstalling the whole operating system.