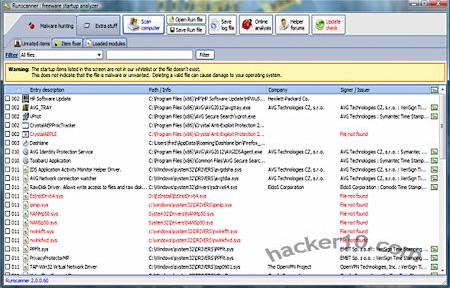
Runscanner is a free antispyware utility that will scan your computer for all running processes, it can detect system changes made by malware, like startup programs that show advertisements and ransomware, page hijackers, accidental misconfiguration or garbage left behind by uninstalled software.
It only took a couple of minutes to scan my hard drive and all orphan files, registry keys and drivers, where clearly labelled in red making it easy to identify and select them for subsequent erasing. I could not see any evident false positive, only a few files that I did not know what they were for and I decided to keep them. Before deletion, using the “Fix it” button, you are given a clear warning about making sure you know what those files are.
In advanced mode you will also see a tab called “Extra stuff” where you can edit Windows host file (often modified to show adware), check autostart items, kill processes, see installed software, and restore Runscanner history backups. Reports, using its own .run file extension, can be saved an opened, the tabbed interface has other options like “Unrated items“, “Item fixer” and “Loaded modules“.

The main window helps you distinguish files showing the item name, path, description, company and digital signer if any. When you find a suspicious item right clicking on it will allow you to submit the file for scanning to online antivirus “Virus Total” or look up the file MD5 at File advisor, Google or Runscanner database. Another button gives you quick access to a malware discussion forum where to ask questions.
The advanced mode is potentially dangerous unless you understand what many of the files showing up in the window are, deleting something by accident could render your computer unbootable or without Internet access, the beginner mode only has the “Scan” an “Update” buttons visible, with no tweaking options, making it very hard to cause damage.
Runscanner has many more features than the popular HiJackThis system analyzer, or Process Hacker, it is a good alternative to them and I would consider this tool for those who have already been infected or just want to make sure that everything is working as it should.